Smartphones, ransomware and Microsoft Office macros are featured in this week’s cyber security news. The post covering cyber security and the Ukraine Russia conflict has be updated several times this week – make sure you are aware of the latest developments and have actioned the National Cyber Security Centre’s advice, linked to in the post.
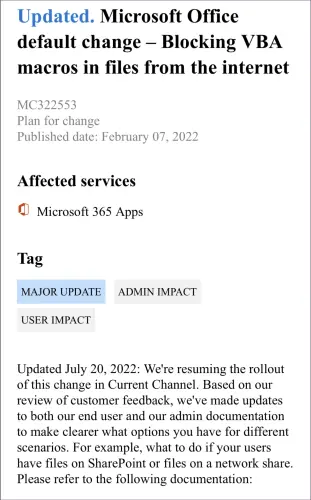
The Microsoft flip-flop story of “to block or not to block” Office macros has (hopefully) been resolved this week – with the “blocking VBA macros in files from the internet” being the default. (I have written an article for the cyber security training website CyberAwake, looking at the good, the bad and the ugly around the issue of macros – it is due to be published next week, and there will be a link in next week’s round-up.)
Smartphones have always been a target for threat actors, highly capable, internet connected computers, constantly in the hands of many people who do not truly understand security or privacy – loaded with all of their personal and private information! In the past few weeks there appears to have been a rush of malicious apps discovered in the Google Play Store and iPhone users are not exempt, there is Pegasus and Hermit spyware for high value targets and text message phishing campaigns for the rest of us.
Ransomware stories this week cover, free ransomware software available for less skilled threat actors, the malware author just wants 20% of any ransoms collected to ransoms being returned by law enforcement agencies. You need a cyber security plan to avoid being a ransomware story. To go with that cybersecurity plan you need an incident response plan – I know that next week’s staff training at Octagon, is being run by Martin, our operation’s manager and he is going to be running through an aspect of our incident response plan, to check we are prepared. That is the type of incident response plan you need.
The “Because IT’s Friday” post this week is back in space.
This is a weekly round-up of the articles from Smart Thinking Solutions, our specialist cybersecurity, governance and compliance web site.
The articles are mostly quick reads to give you an overview of the cybersecurity threat landscape facing businesses today, with links to the sources. Many of the posts have action points or top tips to help you navigate these threats to your organisations.
Sometimes they are just there to make you smile!
Clive Catton MSc (Cyber Security) – by-line and other articles
Because It’s Friday – back to space this week
Zero-day targeted attack against journalists using Google Chrome
US Cybersecurity and Infrastructure Security Agency advisories on security updates – Chrome, Oracle, Drupal, Apple, Cisco and Atlassian
More ransomware money returned – but your cyber security plan should not depend on that. Do you have a cyber security plan?
Social engineering – your trust abused on YouTube
If you hold a little or a lot of sensitive data in a web app make sure it is secure!
Ransomware attacks delivered and monetised with little technical knowledge
Targeted Mac attacks – CloudMensis
Belgium the target of Chinese cyber attacks
And it’s back – Microsoft reinstates, default blocking in Office apps of macros from the internet.
Here’s something new from SANS – Apple Patches Everything Day”
Roaming Mantis targets both Android and Apple iOS. But there are more malicious apps out there than you probably realise…
Pro-Ukraine activists targeted by Russian hackers
Air-gapped systems used to be among the most secure IT systems – but they may be not anymore…
US Cybersecurity and Infrastructure Security Agency issues an advisory on fleet GPS tracking units
More warnings about the possible spread of the Russian Ukraine cyber-conflict and NATO members are targets.
Who decides who the good guys are? Don’t worry though NSO only sells it’s spyware to approved governments and law enforcement agencies
Now bad reviews are becoming a cyber criminal’s choice of attack UPDATED 20 July 2022
CISA advisory for continued exploitation of Log4Shell in VMware Horizon Systems
Cyber attacks on governments large and small
More problems with July’s Patch Tuesday
Facebook believes in privacy but will not let you strip tracking from its URLS
How secure is your WordPress website and blog? Do you even know if your organisation’s website is built on WordPress?
Is there censorship on the web?
Cloudflare updates us about the massive DDoS attack they held back
Here is the reason why patching and updating of any software is essential. Do you want the reassurance that all the updates are being completed across your organisation?
Tor browser can now give privacy and evade censorship barriers
Industrial systems as targets for threat actors – this why you need a software policy. Do you have one?
Hacking everywhere – even if you use MacOS
Here are a couple of background stories on privacy
LendingTree suffers a data breach
Journalists are among the targets of state sponsored hacking and espionage
OpenDocument files distributing stealth malware – make sure your team can recognise these types of attack.
H0lyGh0st ransomware targets small and medium businesses
Anonymous browsing – not anymore
Because It’s Friday – A guide to computer terms from 1981 and good advice for computer users in 2022


